Featured Topics
Featured Products
Events
S&P Global Offerings
Featured Topics
Featured Products
Events
S&P Global Offerings
Featured Topics
Featured Products
Events
S&P Global Offerings
Featured Topics
Featured Products
Events
Financial and Market intelligence
Fundamental & Alternative Datasets
Government & Defense
Professional Services
Banking & Capital Markets
Economy & Finance
Energy & Commodities
Technology & Innovation
Podcasts & Newsletters
Financial and Market intelligence
Fundamental & Alternative Datasets
Government & Defense
Professional Services
Banking & Capital Markets
Economy & Finance
Energy & Commodities
Technology & Innovation
Podcasts & Newsletters
19 Feb, 2026
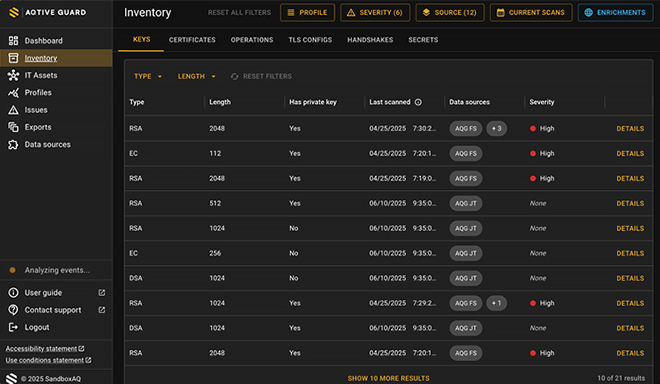
| The Sandbox AQ interface uses AI to evaluate and triage vulnerabilities. Source: Sandbox AQ. |
➤ The US Department of Defense struck a five-year contract with Sandbox AQ to shore up security before quantum computers break current encryption.
➤ Sandbox AQ
➤ Experts predict quantum attacks could become a reality sometime between 2029 and 2035.
Sandbox AQ recently secured a five-year contract with the Defense Department's chief information officer to deploy its AQtive Guard platform across the Pentagon. The deal positions the cybersecurity company to help the military inventory cryptographic assets, identify vulnerabilities and automate remediation before quantum computers can break current encryption standards — what the industry calls Q-Day.
S&P Global Market Intelligence spoke with Sandbox AQ COO Andrew McLaughlin, who previously served as deputy chief technology officer in the Obama White House and spent a decade at Alphabet Inc.'s Google LLC. McLaughlin co-founded Sandbox AQ in 2022 as an Alphabet spinout focused on quantitative AI and quantum-related technologies.
What follows is an edited transcript of that conversation.
S&P Global Market Intelligence: Can you tell us why this DOD partnership is significant for Sandbox AQ and how it changes the quantum cybersecurity landscape?
 Andrew McLaughlin, COO of Sandbox AQ. Source: Sandbox AQ. |
Andrew McLaughlin:
A couple months ago, we launched a revamped SaaS [software-as-a-service] platform for quantum defense called AQtive Guard. It's designed to insulate customers against quantum attack while addressing a broader problem: any scaled enterprise with cobbled-together legacy systems will have out-of-date certificates, keys that are too short, cryptographic standards that don't work — just vulnerabilities in cryptography. The product is a unified oracle that tells you what cryptography you're running in all its different forms. You need to know what's out there, what's being used, in your own data centers and in the cloud.
I use this analogy: If you're protecting a house, everywhere there's a lock is like cryptography. Locks on doors, drawers, jewelry boxes, closets, bathrooms. You need to know what the locks are, where they are, what they're protecting. Then imagine two kinds of burglars: the normal burglar trying to find vulnerabilities like a combination lock still set to 12345, and this new kind of burglar with a quantum key that can open any lock.
Our tool does the inventory from all different sources, pulls it into one view, uses AI to prioritize the work. We show you critical vulnerabilities, less critical ones, ones you can relax about. Looking ahead, we can do automated remediation — automatically upgrade a particular kind of certificate or cryptography to the NIST standards for post-quantum cryptography.
What's the timeline for quantum attack becoming a reality?
The outer skeptical prediction is 2032 to 2035. Increasingly, we're seeing this hockey stick of scientific achievement in quantum computing moving that date forward. The Canadians have said 2031, Singapore said 2029. The Israeli bank regulator has told banks they have to upgrade by 2029. The question is: Do you want to be aggressive or not?
The Defense Department doing this deal with us for inventory, analytics and automated remediation — they're saying we need to get ready now. We shouldn't wait and take chances that we can blow it off for a couple years. They're saying we need to get this done now. From a national security standpoint, it's a good decision.
How does quantum networking infrastructure fit into this picture?
We try to maintain visibility into US and European quantum companies, and we pay attention to Chinese quantum research efforts, which are much harder to track. It's clear there are tens of billions of dollars being dedicated to quantum computing in China across different modalities.
If you're a bank, if you're bitcoin, if you're the US military, you've got to assume two things are true: Your cryptography is going to be breakable unless you upgrade it, and AI agents good at doing tedious stuff are being unleashed to find vulnerabilities much faster than any human hacker would.
How does AI security factor into your platform?
The US government is like any enterprise — under pressure to roll out AI for its employees, for the supply chain, for citizens and residents. Everyone interacting with the government. There's pressure to use AI to do things more efficiently. What we've been building is using this cryptography surface as an excellent place to do AI security.
There are three kinds of AI security: One is AI you're running internally in your data centers or cloud — internal AI that needs to be secured. Two is all the third-party tools — ChatGPT, Gemini, stuff your employees are using, either authorized or not authorized. Even if it's authorized, they might be using it in unauthorized ways. Three is all the non-human AI things coming into your network from outside, asking to do transactions, get access to data, download things. They've got credentials from a partner that look legit, but they're not really human.
The DoD CIO's office has been really leaning into this problem. It's great to take advantage of AI, but then you have to secure it in all three areas. That's what we're going towards, because cryptography is this place where you can say who actually gets access, authorization, permissions. It's good the government is starting to pay attention and take it seriously.
How do you view the government's role as AI development accelerates?
The pace of AI is bewildering, and that's not going to change.
In the security area, NIST has been awesome. NIST has done an amazing job building Post-Quantum Cryptography standards to protect against quantum attack. They're a total role model of how you can see what's happening, focus on your lane and jumpstart really vital work that benefits everybody. The NIST standards are going to be the global standards because they're so good at what they do — good at the process, substance, implementation.
The national labs do amazing work on the research side. The US Department of Energy is actually pretty good at supporting commercialization.
My point is: I'm a private sector person running an AI company, and I can't keep up, much less somebody in a government agency. The challenge on the government side is to be ruthlessly prioritized about what you actually need to do for both security and taking advantage of it for your teams. Regulation is sort of a strange way to think about it, because it's so unclear exactly what to regulate, since we don't really know what the technology is going to be like in a year. I don't say that because I'm allergic to all regulation. It is a real conundrum to try to figure out strategically what are the goals you're trying to achieve and what is the mechanism by which to achieve them.